babuino
Hardware-isolated sandbox for AI-generated code. KVM-based micro-VM. Mathematically impossible to escape.
Technical Architecture: KVM vs Docker
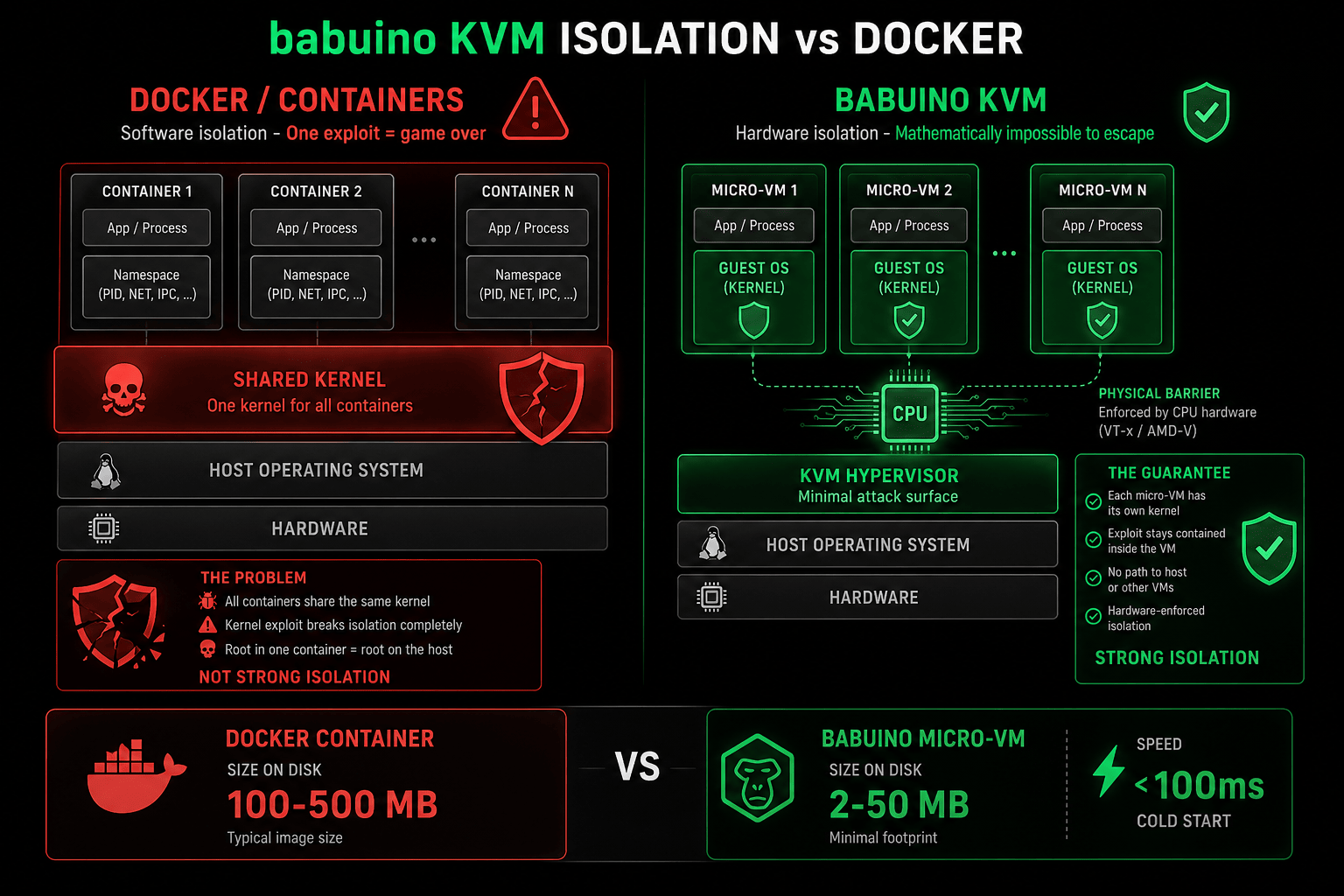
Why hardware isolation matters: Docker shares one kernel. One CVE exploit = access to all containers and host. babuino uses KVM: separate kernel per VM. Physical CPU barrier. Mathematically impossible to escape.
AI Hallucinates. Containers Don't Stop It.
Docker/Podman use namespace isolation (software). One kernel exploit = game over. babuino uses KVM hardware virtualization. Physical CPU barrier. Can't be escaped.
Features
🔒 Hardware Isolation
KVM virtualization, not namespaces. Separate kernel per VM. Exploit in sandbox = contained.
⚡ Micro-VM
2-50 MB footprint. Docker = 100MB+. Spin up 100+ VMs in 16GB RAM.
🚀 Instant Spin-up
<100ms cold start. Pre-warmed pool for 0ms latency. Feels like containers, security of VMs.
📊 Ephemeral
Fresh VM per execution. No state pollution. Previous AI hallucination can't affect next run.
🎯 AI-Optimized
Designed for AI-generated code. npm install, pip, cargo all sandboxed. Typosquatting = blocked.
🔌 Drop-in Replacement
Works with Cursor, Windsurf, Claude Code. Or CLI: babuino run "npm install"
Need Enterprise Features?
babuino is free and open source (MIT). For enterprise-scale orchestration with SLA support, check out Marisma (Enterprise execution platform).
Stop Trusting Containers
Hardware isolation or nothing. Install babuino in 5 minutes.